FBI drops Apple case after cracking iPhone
Dear FBI—
I understand that sometimes government is slow to get technology right. And I fully sympathize; it’s hard to keep up with all the trends and new gadgets and accessories. Everything changes so quickly these days.
But this news is disappointing. It’s just wasteful. Those iPhones are expensive. I know; I have one. What with this being an election year, all the candidates are promising to cut waste. It might not be too long before you can’t even get a new iPhone if you damage the old one.
Don’t worry. This one is pretty simple to explain. You almost had it right, you just got the steps in the wrong order.
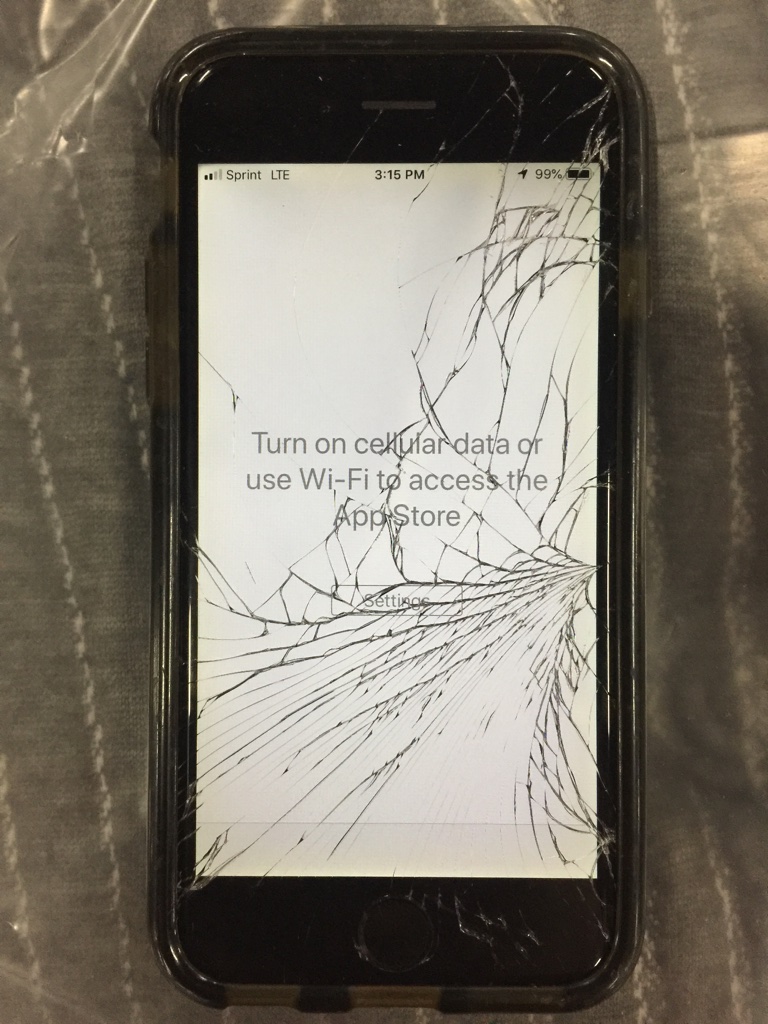
If you put the iPhone in the Apple case first, then the phone won’t get cracked when you drop it.
Also, I don’t recommend dropping it, if you can help it.
Good luck!
Apple
I love the multi-layered puns!
On a serious note, I think Apple blew it. They had a huge marketing windfall in being able to say, “Our software is so secure even the FBI can’t crack it. Relax knowing that your data is safe with us unless you are a mass-murderer.” Now what do they say? “A guy can walk in off the street and crack one of our phones in 28 minutes.” (allegedly)
And after refusing to help the FBI in a terrorist case, they are demanding that the FBI help them fix their software so they can’t do it again? Big brassy ones!
The crack taking 28 minutes
The crack taking 28 minutes doesn’t surprise me in the least. This is no cryptographic hack. It is merely a means of circumventing the four-digit passcode which provides entry to the phone. Apple’s design introduces ever-increasing delays between wrong attempts: get your passcode wrong once and you are asked again within a second. The second time might be two seconds, then five seconds and so on. IIRC, after eight wrong guesses at the PIN the interval is an hour. Optionally after the tenth guess the iPhone can erase itself.
Once this system has been circumvented, a four-digit code can be brute-force hacked quickly. The fact that the crack took nearly 28 minutes indicates to me that they are still using a device that physically taps the numbers onto the touchscreen. Otherwise 10,000 iterations should be possible in less than a second.
I don’t think that Apple needed to say anything at all; it is obvious that the FBI seemed unable to crack the phone. Perhaps by helping the FBI destroy the security measures they could have kept the crack somewhat quieter, but we’re probably more secure knowing about the crack.
I assume that Apple probably knows how the passcode was circumvented; I can think of a couple ways to do it, but it would require me to access or reverse-engineer proprietary Apple technology. If Apple is interested in how the crack was performed, I wouldn’t be surprised if patent infringement and/or DMCA suits followed.
PS
Now I see the FBI has sent a letter to every law enforcement agency in the country offering to help unlock iPhones as long as the PD follows proper procedures as to warrants, etc.
Proper procedure
What troubles me is the question of what constitutes proper procedure.
The courts have already ruled that law enforcement can require a suspect to unlock a phone with a fingerprint reader, though they cannot make that demand with a PIN-locked phone. A PIN is information, whereas the phone itself is physical.
If all a law enforcement agency needs is physical possession of the phone of someone who has been arrested (but not charged) said «proper procedure» requirement seems hollow.
Security
Relying on Apple’s (or anyone else’s) four digit password or the court system is not security. If you want security, encrypt your own files with audited open-source encryption.
Needles and PINs
[quote=Dad]Relying on Apple’s (or anyone else’s) four digit password or the court system is not security.[/quote]
Indeed. But there are always compromises of one sort or another. How are you going to read your public-key encrypted messages on your phone without the private key to decrypt those messages?
Answer: You don’t. You use a private key that has itself been encrypted with a difficult-to-remember 40+ character passphrase. And store that passphrase in a password manager so that it can be copied and pasted. That password manager’s vault isn’t flying around the internet, so you can have an easier to remember and type password on that. And the phone itself is physically in your possession, so long as that is true (and you have the capability to remotely wipe the phone if it leaves your physical possession) slowing someone down is really all you should need.
But it ought to *actually* slow an attacker down. Four digits without an intermediate delay can be cracked in a few hours by someone with fingers, patience, and the ability to count to 9,999. I’ve done it. Don’t ask why. 🙂
Point is, the only perfect security is destroying the information, which makes it useless. There ain’t no perfect security, which is why Zimmerman named his famed encryption software Pretty Good Privacy.